“He who controls the present, controls the past. He who controls the past, controls the future” – Orwell, 1984
Looking back at the last few years, we’ve made some huge leaps at swatting at issues that bit us in back in the past, but still have not made a huge fundamental leap to controlling the future, and in particular controlling the risk from VALUE attacks, such as phishing, crime ware, and process issues (aka business logic issues).
I’ve been interested in process issues for a long time as its the easiest way to get VALUE out of a system. One the earliest web app sec attacks was against CDNOW back in the mid 90’s. They preceded and were bigger than Amazon for a long time. Ultimately, Amazon acquired CDNOW. Why? Apparently, they had a cool front end shopping cart, a payment system and a shipping system. Sure enough, the shipping system took a bunch of hidden fields and accepted a “paid=yes” type of flag. So essentially, you could fill in the hidden fields with the CDs you wanted and skip ahead to the ship bit, and get free stuff. End of story, they’re part of Amazon today instead of the other way around. The opportunity cost of being insecure for CDNOW can be measured in billions and will continue to rise as the years go on. That one attack wasn’t the end of the business, but it set them along the path.
So why in 2009 we do we allow 1995 era attacks to succeed? Why is this stuff not taught at University? Why are the business folks who make really bad decisions allowed to continue on doing the same old, same old, when they should know – do know – that it’s going to cost them a lot more in the long run?
So let’s look at the lows and highs of 2008:
Highlights of 2008:
- PCI compliance starts to hit merchants. They still suck, but they’re unlike before, they’re now going to have to fix their stuff or go out of business
- PCI 1.2 updated to OWASP Top 10 2007. Awesome.
- OWASP has a huge security summit in Portugal, deciding on future directions, and an awesome set of security conferences around the world. I think we have hit critical mass
- OWASP Application Security Verification Standard Released
Low lights of 2008:
- Phishing and malware links as tracked by APWG rose to its highest level ever.
- Massive compromise of credit cards continues – vendors continue to flout PCI regulations and common sense.
- SQL injection attacks launch a million malware infestations
This basically means that attackers have been noted by the mainstream media and others as attacking VALUE through web apps, and not assets, like pwnage. They don’t care about the mechanism so much as the money. This has been my view for at least five years. I don’t care about if you control a 100,000 bot fleet – your just desserts are coming soon in your very own dawn raid. I do care if you can steal from 95,000,000 folks or defraud thousands with one e-mail.
“How’s that working out for you?” – Dr Phil McGraw
When we do something that is clearly not working, it is beyond time to do something different.
Back in 2002, I was doing security architecture in web apps for some of my more forward thinking clients. I have a draft book in my OWASP folder on Web App Security Architecture I started in 2003. When I moved to the USA in 2006, security architecture was completely off the average US enterprise architect’s radar. Only today are seeing some traction in this space, and not everywhere.
Success stories elsewhere
With air safety, various safety bureaus review crashes and make binding resolutions on pilots, manufacturers and airlines to remediate design issues and human factors. For example, in many cultures, a strong hierarchal society is the norm. More than a few co-pilots have sat meekly by, refusing to override their captain as they plowed straight into the ground. So the airlines were forced to change the human element in the cockpit, forcing sub-ordinates to take control when the situation warranted it.
Air safety is a poster child for what can and should be done. From the early days when cowboys ruled the roost and many died, to today when only rail is safer per million passenger miles, air travel is one of the safest transport forms, despite being so inherently dangerous from a physics point of view (speed, height, traffic density, weather conditions, etc). We need to emulate air safety. Web application security is at the point where enforceable regulations are in their early days, like seat belts in cars were 50 years ago.
We can and must skip 50 years. I’m not a huge fan of heavy handed regulation as I feel it will stifle the next big thing if done wrong, but I think many languages and frameworks are settling around a few major paradigms. We can help them, and they must help their users.
We KNOW how to secure those meta-issues. We MUST secure those meta-issues. So here’s my 2009 Wish List:
Education
We have to educate those who come after us. This means getting into every CS and Software Engineering course world wide, and ensuring they have at least one mandatory security architecture / software security subject.
All applications share exactly one feature: security. I don’t think you can be a sound practitioner unless you have at least heard about this most fundamental of issues. It’s like graduating accountants who have not completed Audit 101. It’s completely ridiculous that there’s no equivalent in most CS and software engineering degrees today.
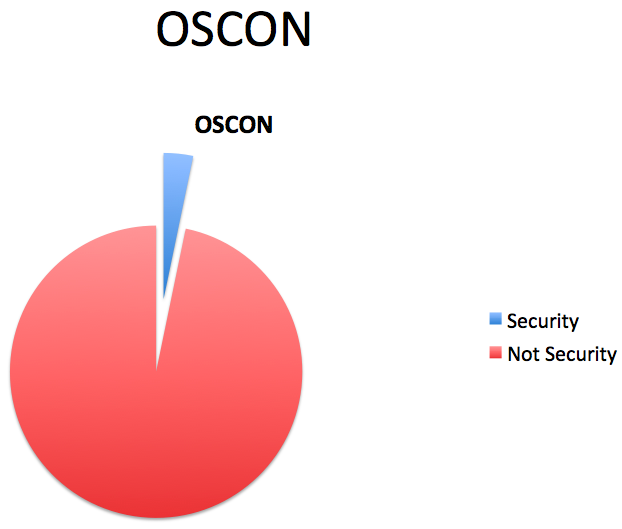
I am also only going to speak at developer and architecture conferences. Speaking at security conferences is awesome and I usually get married or drunk or both, but it really doesn’t advance the state of the art. Architects and developers must get on board, and to do so requires their buy in.
Eliminate XSS and SQL injection
We really need to get some basic technical things off the radar, so in 2010 and beyond we can deal with VALUE attacks. To that end, 2009 should be spent encouraging open source and vendors to fix XSS and SQL injection. We know how to fix these things. OWASP’s ESAPI has the canonicalization, input validation, and output encoding features that every application can use. Every modern framework has prepared statements or a safe(r) mechanism than dynamic statements.
I encourage the OWASP leadership and those in leadership positions to take a stand on these two items. I call on all framework providers to make the simplest possible output mechanism XSS safe. I call on framework providers to deprecate and eliminate dynamic SQL queries, or at least make serious warnings pop up so that folks know that they should not be using those interfaces. I call on open software reporsitories to stop downloads of packages that have open CVE entries. It’s important to bubble up the importance of safe software, and we can’t do this by wishful thinking.
We can do this. It’s not a pipe dream.
Security Architecture Is a First Class Citizen
It’s important to start putting security architecture in its place – which is every bit as important as the shiny buttons folks click or the processes businesses use to get stuff done. We cannot hope to eliminate design issues that allow VALUE attacks unless security architecture fu is strong within every organization writing software today.
Although history is written by the victors, we’re a long way from victory. Let’s get cracking!